Security Modelling
As authors and leading exponents of the SABSA Security Overlay for ArchiMate, CEM is uniquely equipped to integrate the security perspective into your Enterprise Architecture model, regardless of which tool you use.
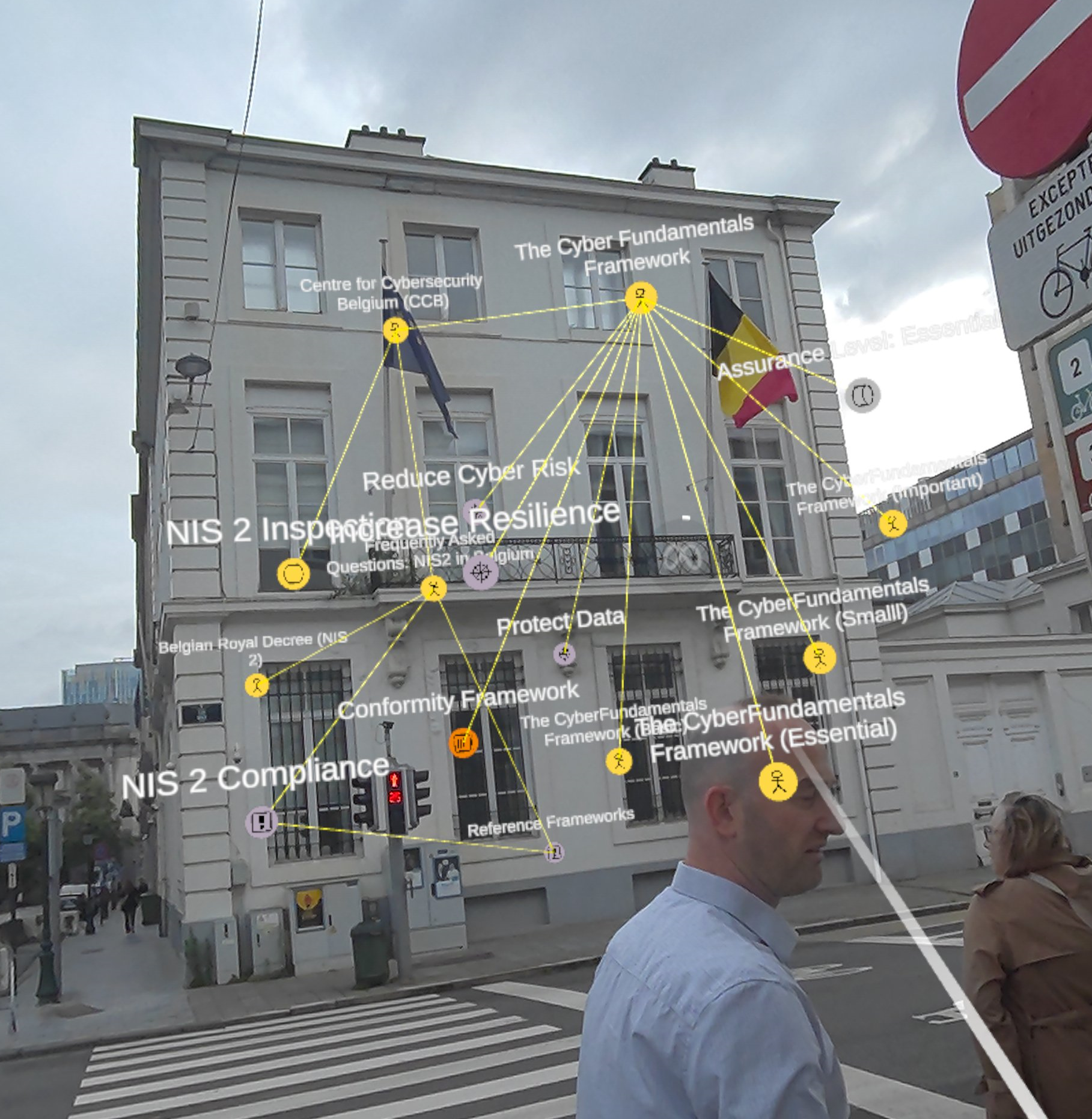
Interactive Visualisation
Step into Your Model
Instead of static diagrams to describe security architecture, a Model-Based Systems Engineering (MBSE) approach offers multiple ways to present stakeholder viewpoints. This can range from the automated generation of reports, such as security analysis, reporting, compliance posture, but it also enables you to step into the model—quite literally.
Discuss your cyber security needs
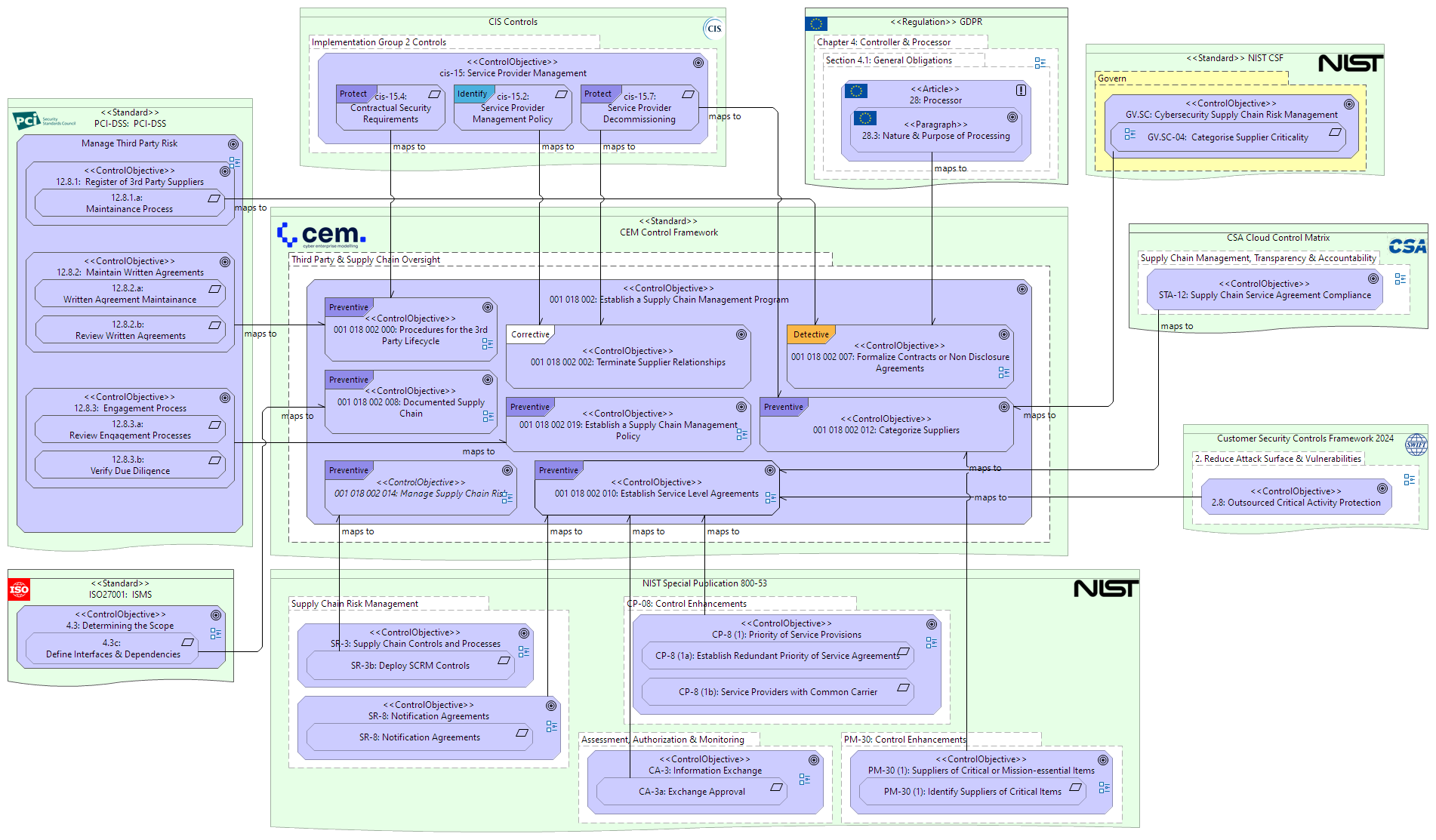
Control Framework Integation
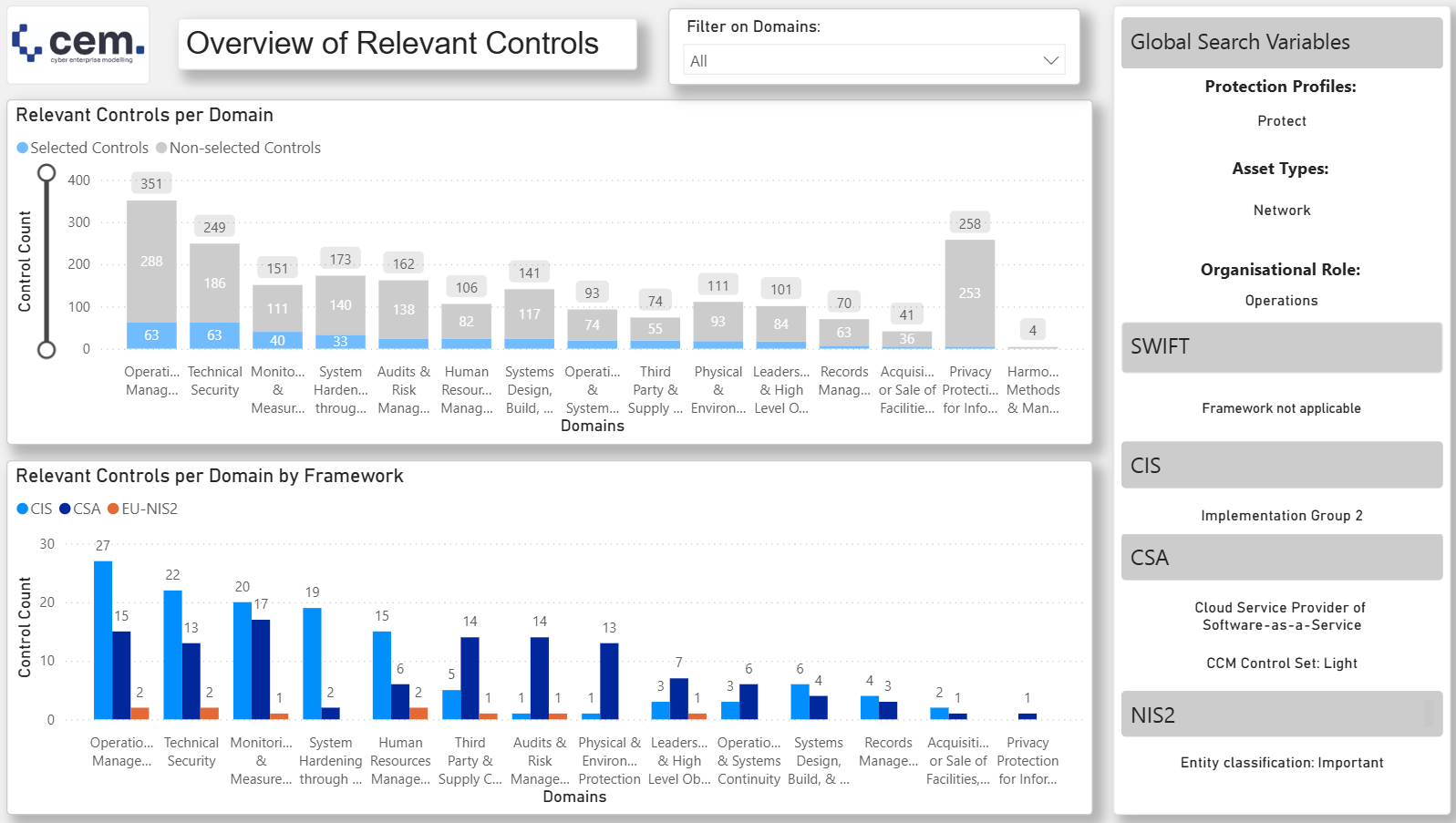
By normalising diverse regulations and frameworks into a common format, it is possible to create a fully-integrated and meta-data enriched platform of security controls.
This can be used to identify, from the thousands of controls in the model, those that are precisely in-scope and applicable to a given stakeholder group and context.
SABSA Enablement
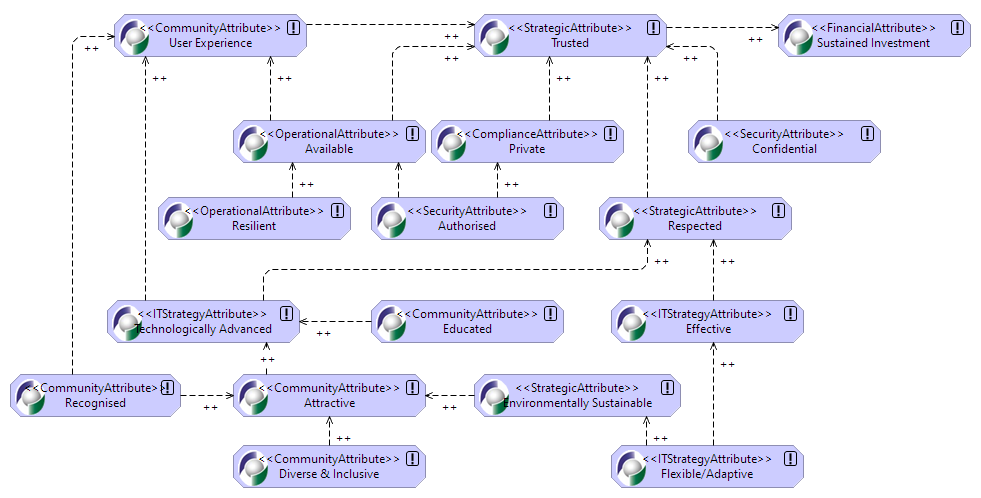
CEM Founders were instrumental in the development of the SABSA Security Overlay for ArchiMate: a means of creating the artefacts produced by the powerful SABSA methodology using the same Enterprise Architecture tools used to describe the target architecture.
Security Architecture is a perspective on the functional architecture, not separate from it. It is highly beneficial then, to document it using the same models and tooling.
Our Services
NETWORK
The most advanced NDR solution
Leading AI-powered cloud email security
CLOUD
Secure your cloud in real time
IDENTITY
Outsmart identity threats across all your apps